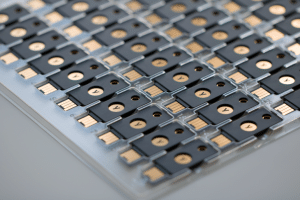
FIDO U2F


The aim of this standard is to make a strong, yet easy-to-use authentication device available to the general public.
This standard is currently managed by the 'FIDO Alliance'.
The Yubikey FIDO U2F has been successfully deployed on a large scale by services such as Facebook, Gmail, Dropbox, GitHub, Salesforce.com, the British government and many others.


Yubikey FIDO U2F provides strong authentication over USB, NFC, Bluetooth in password / tokenless applications
U2F is an open authentication standard that enables users to securely access a wide range of online services with a single device, instantly and without the need for drivers or client software.

The advantages of the U2F standard
Enhanced security - Strong two-factor authentication, using public key cryptography, to protect against phishing, session hijacking, man-in-the-middle attacks and malware.
Easy to use - Works immediately thanks to native support on all platforms and browsers (Chrome, Opera, Mozilla, etc.), enabling instant authentication to a wide range of services. No code to type, or drivers to install.
High privacy - Allows users to choose, own and control their online identity. Each user can also choose to have multiple identities, including anonymous (no personal information associated with the identity). A U2F device generates a new key pair for each service, and only the service stores the public key. With this approach, no secrets are shared between service providers, and even low-cost U2F devices can support an unlimited number of services.
Multiple choices - Open standards offer flexibility and product choice. Designed for existing phones and computers, for a wide range of authentication modes (keychains, direct integration into IT equipment, etc.), and with different communication methods (USB, NFC, Bluetooth).
Interoperable - Supported by major Internet and financial services. U2F allows each service provider to be its own identity provider, or to provide users with the option of authenticating via a federated service provider.
Cost-effective - Service providers don't have to bear the cost and support of secure distribution of U2F devices. Users can choose from a range of low-cost devices from several suppliers, available from Amazon and other retail stores worldwide. Yubico offers free, open-source server software for back-end integration.
Electronic identity - For organizations that require a higher level of identity assurance, services are available to associate your U2F device with your true identity, both online and offline.
Secure recovery - Users are recommended to register at least two U2F devices with each service provider if a U2F device is lost. Services can also provide users with a backup code, which they store in a safe place.
Yubico products are ready to use with hundreds of services and applications for personal and professional use. Scroll through the logos to see detailed instructions for each service. Click here for more information.
YubiKey with Google accounts to access Gmail, Google Apps, YouTube, Google+. YubiKey with Facebook makes it an "Official Facebook" by telling your friends and followers that you're using YubiKey so they can trust that it's really you who's posting.
YubiKey with Salesforce for IT administrators to prevent unauthorized access to the Salesforce.com platform. YubiKey with GitHub to access developer repositories, including using U2F over NFC on Android phones.
USE YubiKey with Dropbox to access YOUR DATA your data stored in the cloud.
The U2F certificate
The purpose of U2F attestation is simply to provide a mechanism for a U2F Relying Party (a Web site or service) to verify the authenticity of a U2F authenticator and thus trust its attestation certificate. A Relying Party queries the attestation certificate for information about an authenticator, such as a YubiKey.
The information requested may include the supplier, device type and assurance/security properties (e.g. a secure element-based device) of the authenticator. The authenticity of attestation information is guaranteed by a digital signature with a specified validity period.
In addition to certifying the authenticity of a device, the attestation certificate can also be used to determine which devices can be used by a user party. For example, a banking site may want users to be able to provide their own U2F devices for two-factor authentication, but only allow users to use devices from certain approved suppliers.
However, there is no requirement to dictate what type of client-side device or software uses U2F - the trusted party or service can decide to accept any type of attestation certificate or a specific type.
Buy your Yubikey FIDO U2F NFC now!