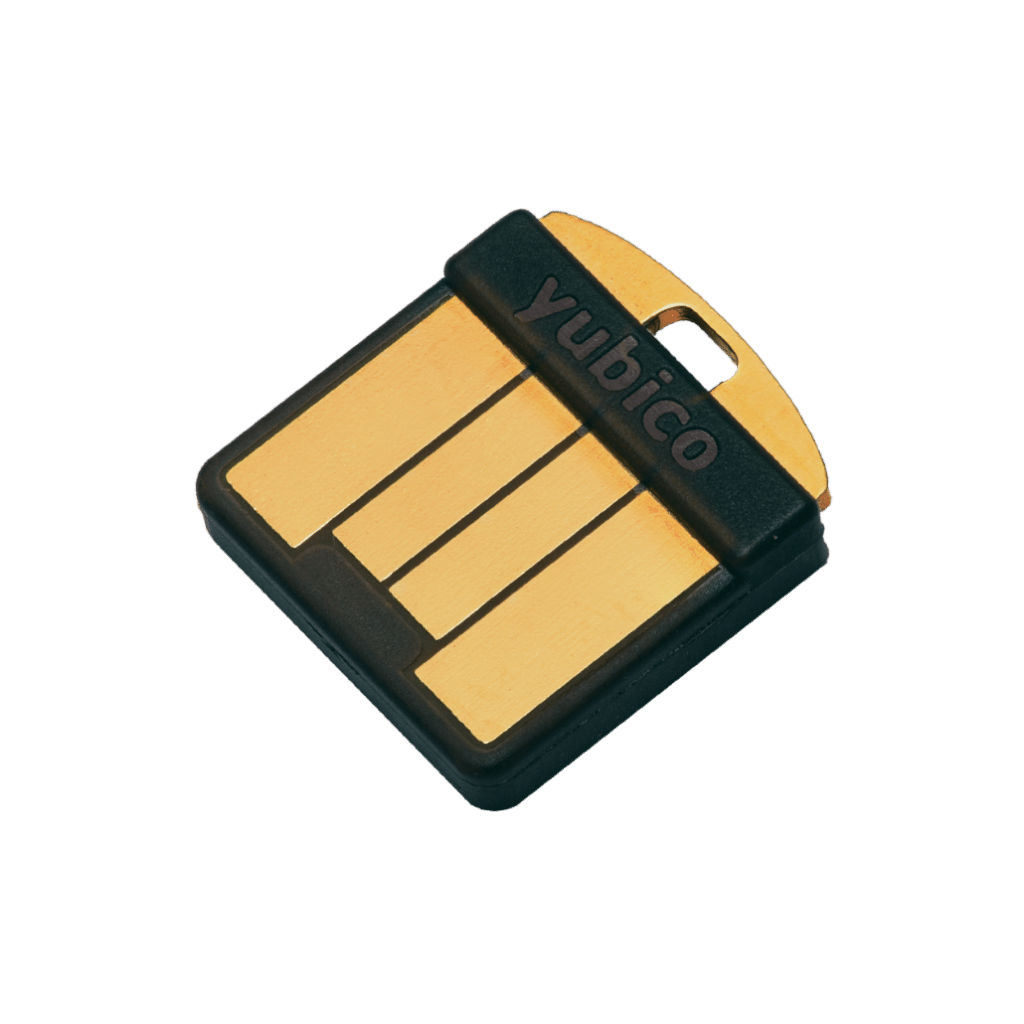
YubiHSM 2
YUBICO
YubiHSM2
Best price/performance hardware security module


Trusted root for servers and peripherals
YubiHSM 2 is a cost-effective hardware security module (HSM) for servers and IoT gateways, offering advanced digital key protection features and benefits at a price that is accessible to all organizations.
It provides the highest levels of security for cryptographic digital key generation, storage and management, supporting a wide range of enterprise environments and applications. YubiHSM 2 features are accessible via Yubico's Key Storage Provider (KSP) for PKCS # 11 or Microsoft's CNG, or via native Windows, Linux and macOS libraries. Its ultra-thin "nano" form factor fits inside a server's USB port, eliminating the need for bulky additional hardware and offering flexibility for offline key transfer or backup. Essential security functions, including hashing, asymmetric and symmetric cryptography to protect cryptographic keys at rest or in use. These keys are most often used by certification authorities, databases and code signing to secure critical applications, identities and sensitive data within an enterprise.

Securing Microsoft Active Directory certificate services
YubiHSM 2 provides a hardware-secured key to secure digital keys used in a Microsoft-based PKI implementation. Deploying YubiHSM 2 in Microsoft Active Directory certificate services not only protects the root keys of the certification authority, but also protects all signing and verification services using the root key.
Enable hardware-based cryptographic operations
YubiHSM 2 can be used as a complete cryptographic toolbox for a wide range of open source and commercial applications. The most common use case is hardware-based digital signature generation and verification.
Improving the protection of cryptographic keys
YubiHSM 2 offers a compelling option for the secure generation, storage and management of digital keys, including essential capabilities for generating, writing, signing, decrypting, hashing and packaging keys.
Feature overview
Secure key storage and operations
Extensive cryptographic capabilities: RSA, ECC, ECDSA (ed25519), SHA-2, AES
Secure session between HSM and application Role-based access controls for key management and key usage 16 simultaneous connections
Optional, network can be shared
Remote management
Unique "Nano" form factor
Low power consumption
Backup and restore key M from N
Interfaces via YubiHSM KSP, PKCS # 11 and native libraries
Tamper-proof audit logging
Extended cryptographic capabilities YubiHSM 2 supports hashing, key encapsulation, asymmetric signing and decryption operations, including advanced signing using ed25519. Attestation is also supported for asymmetric key pairs generated on the device.
16 simultaneous connections
Multiple applications can establish sessions with a YubiHSM to perform cryptographic operations. Sessions can be automatically terminated after inactivity, or can be of long duration to improve performance by eliminating session creation time.